25 Major Cyber Attacks in India: Threats and Strategies
Home / 25 Major Cyber Attacks in India: Threats and Strategies

TECHNOLOGY
Mar 3, 2026
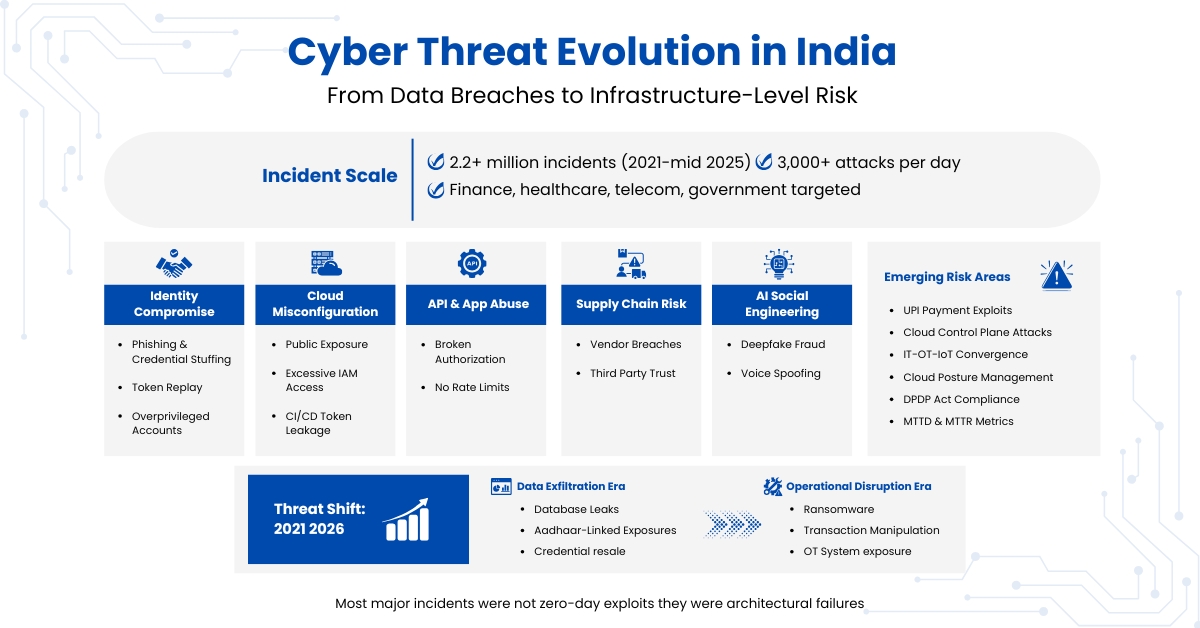
India has seen a sharp rise in cyberattacks over the last few years, which has turned data protection into a top security concern. According to CERT-IN, between 2021 and mid-2025, India recorded more than 2.2 million cybersecurity incidents, averaging more than 3,000 attacks per day, with financial services, healthcare, telecom, and government platforms among the hardest hit.
Hackers focused on cloud misconfigurations, unpatched servers, and weak internal access controls. The list below tracks 25 major cyberattacks in India from 2021 to 2025, showing how they happened and what strategies can be used to prevent similar breaches.
High-Impact Developments (2025–Early 2026) and Strategic Threat Evolution
Apart from the above-mentioned incidents, the late 2025 and early 2026 threat intelligence reports from Indian SOC service providers have identified three emerging risk categories that are worth mentioning:
- Mass UPI Payment Ecosystem Attacks (2025–2026)
The Indian UPI ecosystem remains under constant attacks through:
- API abuse attacks
- SIM swap fraud
- Real-time social engineering attacks coupled with screen-sharing malware
- Token replay attacks on inadequately validated session flows
Although most of these attacks were prevented before causing systemic damage, it is evident that attackers are now moving from database theft to transaction manipulation attacks.
Strategic implication: Fintech platforms need to incorporate transaction anomaly detection based on behavioral baselining, device fingerprinting, and velocity thresholds instead of only credential verification.
- Cloud Control Plane Exploitation Cases (2025)
Several breach incidents in 2025 involving Indian businesses were found to include:
- Compromised or misused IAM roles
- Overprivileged service accounts
- Unsecured Kubernetes control plane dashboards
- CI/CD pipeline token exposure
In contrast to conventional data breaches, these attacks involve the cloud control plane, enabling malicious actors to provision infrastructure, steal logs, turn off monitoring, and achieve persistence.
Key technical lesson: Security misconfiguration, and not malware, is the leading root cause. There is a need to shift towards:
- Security scanning of infrastructure-as-Code
- Just-in-time privilege escalation
- Continuous Cloud Posture Management (CSPM)
- AI-Powered Deepfake Business Email Compromise (BEC) Escalation (2025–2026)
Sophisticated fraud campaigns now combine:
- Synthetic voice cloning of executives
- Real-time video deepfakes during virtual meetings
- AI-produced legal documents
These attacks will target decision-makers in a way that phishing attacks do not, and they will not be filtered out by technical security.
Mitigation shift required:
- Implementation of out-of-band verification for financial transactions
- Callback verification for high-value transactions
- Integrate deepfake detection capabilities into communication systems
This is not a hypothetical threat, as Indian financial institutions have seen six- and seven-figure fraud attempts using this hybrid approach.
Emerging Systemic Risk: Convergence of IT, OT, and IoT
A rising concern for 2025–2026 is the growing convergence of the following:
- Smart grids
- Industrial IoT sensors
- Healthcare diagnostic devices
- Smart city infrastructure
The attack surface is expanding into operational technology (OT). Current IT controls are inadequate for securing SCADA systems and medical device firmware.
Critical oversight: Too many OT networks still lack properly segmented networks and anomaly monitoring in real-time.
1. Angel One AWS resource breach/potential data leakage, February 2025
Angel One, India's largest broking firm, was recently hacked. Hackers gained access to an unsecured AWS storage bucket linked to it, exposing the sensitive data of 7.9 million users, such as trading details, email addresses, and customer IDs. Cloud management made sensitive data visible on public servers. To avoid such scams, similar companies must audit all cloud buckets, enable encryption, and always restrict public access through IAM (Identity and Access Management) rules.
2. AI-generated Phishing and Infostealer Surge, 2025
In 2025, several Indian banks and fintech platforms reported a rise in AI-generated phishing scams. Attackers used a realistic, AI-written email to fool users into giving away credentials. Thousands have already fallen victim to these smarter phishing campaigns by unknowingly entering their bank credentials, leading to financial losses and identity theft.
Attackers also used voice cloning and deepfake technology to impersonate officials, which makes the deception look more convincing. One must consider the fact that constant user training, spam filters, and AI-based email scanning tools block most phishing messages before they reach inboxes.
3. Aditya Birla Capital Digital (ABCD) App Hack, 2025
Hackers targeted a weakness in the ABCD mobile app API, revealing customers' loan and PAN details. The attackers targeted unprotected endpoints, which allows data scraping. API vulnerabilities remain a growing concern for finance apps. However, routine code audits with secure token validation and regular app updates can stop such data exposure.
4. Star Health Threats, May 2025
Star Health, one of India's largest health insurers, experienced a major data breach that affected 31 million policyholders; much of the core information, including medical records, insurance details, and personal information, was breached and even published on the dark web. This breach shows how healthcare data can be exploited for identity theft. Encrypting health records, segmenting sensitive systems, and ensuring continuous monitoring can reduce such risks.
5. Delhi Hospitals Ransomware Attack, June 2025
Delhi's Sant Parmanand and NKS Super Speciality hospitals were targeted by ransomware that locked almost all patient and billing data. Over 60,000 records were affected by this attack. The attack used phishing emails to deliver ransomware payloads. The malware spread quickly through unprotected hospital networks.
Hospitals should isolate administrative and patient data systems, train staff to identify suspicious emails, and maintain offline data backups.
6. Kolkata Police Cyber Crime Wing Data Breach, August 2025
Weak internal passwords and a lack of access control allowed hackers to access internal police systems, where investigation details from the Cyber Wing in Kolkata were leaked. This breach exposed officer credentials and case data. The attack raised alarms about insider threats and the need for stronger law enforcement cybersecurity.
Police and law enforcement agencies should adopt role-based access control, enforce password rotations, and enable two-factor authentication for internal systems.
7. Multiple Cyberattacks on Indian Governments, 2024.
Multiple state e-governance portals were hacked in 2024, leaking citizen Aadhaar and bank details. At least 2.5 million records were compromised across several platforms. Many portals lacked basic HTTPS encryption, which allowed attackers to exploit outdated plugins and weak admin passwords.
That's why regular CMS updates, secure admin logins, and government-wide cybersecurity policies are vital for protection. Every e-governance platform must undergo quarterly vulnerability assessments and follow a national cybersecurity standard to protect public data.
8. Polycab Ransomware Attack, March 2024
Polycab India, a top cable manufacturer, suffered a ransomware attack, causing a Rs 20 crore operational loss. The breach started from an infected employee workstation and ended with hackers encrypting internal files and demanding high payments. The attack also affected the supplier and distributor network, exposing the ripple effect of industrial cyber incidents.
9. Indian Energy Sector Attack, 2024
This breach shows the exposure of operational technology systems, where hackers tried to infiltrate India's power grid through malware-infected email attachments sent to energy employees. The attack aimed to disrupt the electricity supply but was quickly contained.
Tip: Separating IT and OT networks and constantly monitoring power infrastructure can prevent major outages like this. Moreover, conducting red team simulations and regular cybersecurity drills helps reduce the chance of large-scale blackouts.
10. BSNL Data Breach, May 2024
Personal details of 2.9 million broadband subscribers were leaked from a BSNL database due to old, unpatched systems. Leaked data included phone numbers and service details. The breach came from a neglected internal server. The outdated system, left without proper monitoring, became an easy entry point. Updating infrastructure and restricting admin access can prevent similar service providers.
Read Also: Top 30 Best-Known Cybersecurity Case Studies 2025
11. UP Marriage Assistance Scheme Leak, 2024
The Uttar Pradesh Marriage Assistance Scheme is a welfare initiative aimed at helping low-income families. Data from the welfare portal of Uttar Pradesh leaked, including Aadhaar, bank details, and contact information, affecting 200,000 applicants. The data was found indexed on search engines, shockingly. The root cause was traced to poor web server configuration and missing access restrictions. A web firewall and regular penetration testing could have prevented this from happening.
12. Airtel India Customer Database Leak (375 Million Users), June 2024
Hackers claimed to sell a database of 375 million users, which would be nearly 25% of India's population. Airtel denied the break, but the data was widely shared online. The leak included Aadhaar numbers and personal details. Even if false, it revealed risks from third-party data handling. Telecom companies must run vendor audits and apply zero-trust security across all databases, anonymising customer data wherever possible to reduce exposure if leaks occur.
13. WazirX Hack, July 2024
Crypto firms must use cold wallets for storage and conduct third-party code audits before deploying smart contracts. WazirX, a crypto exchange, was targeted by hackers who were exploiting blockchain smart contract vulnerabilities. Roughly $230 million worth of assets were at risk. This breach clearly highlights that public blockchain code, if left unaudited, can create hidden backdoors.
14. boAt India Data Breach, 2023
Encrypting user data and applying hashed passwords are key to securing e-commerce databases. In 2023, an unsecured server was recently exposed, exposing 7.5 million customer records, including names and contact information. The leak spread on Telegram and hacking forums. Weak password protection made recovery even harder. Many users later reported spam calls and targeted ads due to leaked data.
15. Telangana Police's Hawk Eye App Data Breach, 2023
Hackers accessed the Hawk Eye mobile app, revealing user profiles and feedback reports. The app, meant for citizen safety, accidentally exposed personal data through a misconfigured API. Public-facing government apps should use token-based access, secure API gateways and regular security reviews before each software update.
Read Also: Top 50 Cyber Security Projects for Final Year Students (2025 Edition)
16. Hyundai Motor India Data Leak, 2023
Thousands of car owners whose contact and vehicle details were stolen were found on the dark web. The source of the breach was traced to a third-party vendor responsible for managing the dealer's database.
Weak vendor access controls and outdated security measures worsened the system, risking identity misuse because the data appeared on dark web forums for sale.
17. SPARSH Data Breach, 2023
The Ministry of Defence's SPARSH portal suffered a breach, which exposed pensioner IDs and bank details. Hackers used credential stuffing techniques on weak passwords. This breach raised national security concerns as the portal handled sensitive military data. Multi-factor authentication, stronger password policies, and regular login behaviour analysis can stop similar attacks.
18. Sun Pharma Cyber Attack, 2023
Pharmaceutical giant Sun Pharma's ransomware disrupted its internal operations and supply chain, causing Rs. 30 crore in losses. Hackers entered through a phishing email and encrypted internal servers.
Companies should train employees to identify phishing attempts, install anti-ransomware software, and maintain offline data backups for rapid recovery.
19. BharatPe Hacked: August 2022
Phishing emails led to a breach of employees' inboxes, leaking internal documents and financial reports. The attackers used social engineering to mimic trusted contacts, tricking employees into sharing login credentials. While no customer data was stolen, the breach hurt investor confidence. Using email MFA, spam filters, and awareness campaigns can block future phishing attempts.
20. Cyberattack on AIIMS: December 2022
India's top hospital, AIIMS, suffered a ransomware attack that took 3 million patient records. The servers remained slow for approximately two weeks, which caused major disruption.
Read Also: The Rise of Agentic AI in Cyber Warfare: Implications for Global Security
21. CloudSEK Data Breach: December 2022
In 2022, hackers stole internal data from the cybersecurity firm CloudSEK and exposed API keys on GitHub. The breach revealed how even security companies can be vulnerable. Never use credentials in code repositories, and rotate all access tokens regularly.
22. Swachhta Platform Hacked, September 2022
Hackers breached India's Swachh Bharat (Clean India) platform, a government site that collected public sanitation feedback and cleanliness reports. The attackers took advantage of outdated CMS plugins and weak credentials, allowing them to deface the homepage and delete parts of the citizen feedback database.
23. Zivame Data Breach, 2022
In 2022, Indian lingerie retailer Zivame experienced an excessive data breach exposing personal and transactional information of nearly 1.5 million customers. The data included names, phone numbers, email addresses and partially masked payment records. Investigators traced the cause to an unsecured database server left open to the public without password protection. The leaked dataset appeared later on dark web forums for sale.
24. Air India / SITA Passenger Data Breach, 2021
Recently, in 2021, a global cyberattack on SITA, the IT provider for various airlines, exposed personal data of over 4.5 million Air India passengers, which included passport details, ticket numbers, birth dates, and contact information. The breach was traced to unauthorised access in SITA's passenger service system, which connected multiple airlines worldwide, compromising long-term passenger privacy.
That's why airlines and travel companies must vet all external vendors for compliance with strict cybersecurity standards, enforce encryption for shared databases and deploy continuous threat detection across connected systems.
25. Domino's India Customer Data Leak, 2021
Hackers exposed nearly 180 million customer order details, including their names, phone numbers and even GPS coordinates. Attackers used an unsecured server within the company's order-tracking infrastructure, and later they published the full dataset on the dark web. The exposed location information was essentially alarming, as it could reveal customers' routines and residential details.
Companies handling location-based services should encrypt all customer data, mask stored addresses and set strict retention periods for order records.
Read Also: Zero Trust Security: The Future of Cyber Defense
Root Cause Analysis of Major Cyber Incidents in India (2021–2026)
The extent of breaches can be understood from the list of breaches over time. However, the actual analysis is in understanding the architectural vulnerabilities and control failures that led to initial access, privilege escalation, and operational impact.
The technical vulnerabilities that have been common in major incidents from 2021 to 2026 are quite evident.
- Identity is the Real Perimeter — and It Is Repeatedly Failing
Most high-impact breaches came from compromised credentials, not zero-day attacks. The attack chains included:
- Phishing-based credential extraction
- Credential stuffing attacks based on leaked databases
- Session hijacking attacks based on stolen tokens
- Abuse of over-privileged service accounts
After successful authentication, the attackers moved laterally in the trusted network segments.
The technical gap is not the lack of MFA but the lack of effective identity governance.
Most environments still do not have:
- Privileged Access Management (PAM) vaulting
- Conditional access based on device posture
- Behavioral anomaly detection (UEBA)
- Token binding and replay protection
Identity infrastructure must enforce continuous verification, not just authentication at the time of login.
- Cloud Misconfiguration: Control Plane Exposure
What recent cloud breaches have shown is that there is a much larger problem at play: while companies protect their workloads, they fail to secure the control plane.
Some of the common issues include:
- Object storage buckets left publicly accessible
- Too many permissions assigned to IAM roles (wildcard permissions, for example)
- Access keys hardcoded into CI/CD pipelines
- Unmonitored CloudTrail logs
In some Indian enterprise instances, attackers did not "hack" the infrastructure but instead used automated scanning tools to enumerate publicly accessible resources.
To address these issues, it is necessary to:
- Validate Infrastructure-as-Code security before deployment
- Automatically scan for misconfigurations
- Implement least-privilege IAM role policies
- Continuously rotate keys and manage secrets
Cloud security breaches are rarely complex, they are procedural and governance-driven.
- API-Layer Vulnerabilities and Business Logic Abuse
As fintech and mobile technologies continue to grow in popularity, the API layer has emerged as the primary attack vector:
The type of vulnerabilities that have been identified include:
- Broken Object Level Authorization (BOLA)
- Absence of authentication on internal API routes
- Absence of rate limiting on scraping attacks
- Insufficient validation of the schema
In some instances, attackers have been able to take advantage of logical issues rather than vulnerabilities in the infrastructure, such as iterating user IDs to access sensitive data.
Following are some of the new security requirements that need to be included in API security:
- Traffic analysis at the transaction level
- Behavioral anomaly detection at the transaction level
- Validation of OAuth tokens
- Automated abuse detection against enumeration attacks
- Ransomware and the IT–OT Convergence Risk
Between 2024 and 2026, the trend from data exfiltration to operational impact became more apparent. Healthcare, manufacturing, and energy infrastructure were all subject to ransomware attacks on operational continuity.
Technically, ransomware attacks were spread through:
- Flat network architecture
- Unsegmented backup storage
- Unpatched Active Directory vulnerabilities
- SMB protocol exploitation
In the manufacturing sector, a lack of segmentation between IT and OT networks raise systemic risk.
For them to be effective, mitigation strategies must include:
- Micro-segmentation of the network
- Immutable, offline backups
- Lateral movement detection
- Tight domain controller security
Operational resilience is a designed capability, not an ad-hoc, response to compromise.
- Supply Chain and Third-Party Trust Exploitation
There were a number of high-profile breach incidents that originated from vendor access paths. Attackers exploited:
- API sharing
- Poor vendor password management
- Over-trusted remote maintenance access
The technical difficulty is the extension of trust boundaries. Modern ecosystems are interwoven through SaaS services, cloud connectivity, and managed infrastructure.
Third-party risk scanning, attack surface analysis, and enforcement of minimum security standards are no longer security afterthoughts but security imperatives.
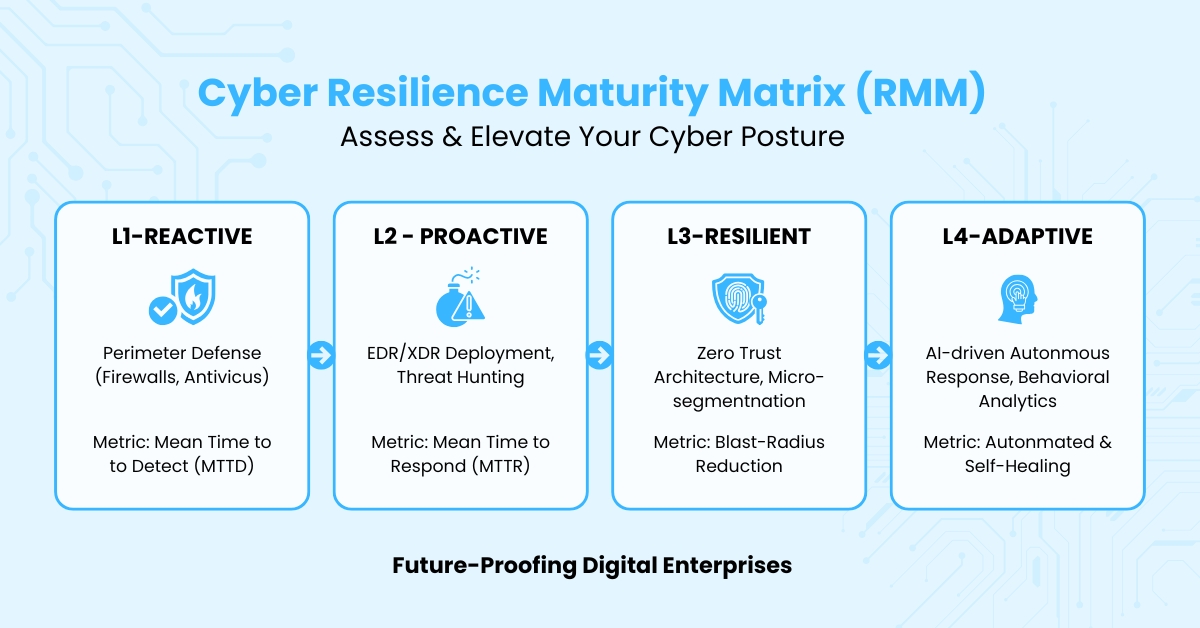
Governance and Measurable Resilience
Cybersecurity maturity cannot be achieved through technical controls only. A resilient system needs to have measurable governance metrics, such as:
- Clearly defined Mean Time to Detect (MTTD)
- Clearly defined Mean Time to Respond (MTTR)
- Continuous adversary simulation and red-team exercises
- Alignment with India's Digital Personal Data Protection (DPDP) Act
Without measurable parameters, cyber readiness will remain a concept on paper. The performance parameters should be able to show the efficiency of containment, recovery, and blast radius reduction.
Actionable Framework: The Resilience Maturity Matrix (RMM)
Organizations can assess their cyber posture across four maturity levels:
Breach Disclosure in the Indian Context
Following factors need to be considered for breach disclosure:
- Compliance with regulations (CERT-In's 6-hour notification requirement)
- Market Sensitivity for NSE/BSE listed companies
- Consequences of identity information disclosure for public safety
Constraints and Realities
There is no such thing as perfect security. The most significant challenge in the Indian scenario is the lack of expertise in cybersecurity, especially in offensive security, digital forensics, and OT security. Additionally, social engineering attacks through UPI scams and messaging services continue to evade sophisticated security measures.
In the End
India's cybersecurity reflects both rapid progress and rising exposure. Attackers have now shifted to multi-stage ransomware, insider misuse, and AI-generated phishing. Organisations that invested early in zero-trust controls, employee awareness programmes, and regular threat monitoring have contained incidents faster and have limited damage. The next step for organizations would be a dependency audit, which would involve mapping reliance on critical digital infrastructure such as UPI, Aadhaar, and ONDC, and identifying third-party trust dependencies before they become breach pathways.
Every sector, private or public, must treat cybersecurity as an operational priority rather than a compliance task tied to reputation, customer trust, and business continuity.
Frequently Asked Questions
What role does artificial intelligence play in cybersecurity?
What is the largest cyber attack ever reported in India?
Which company experienced the biggest data breach in India?
How many cyber attacks occur in India every year?
What are the most common cyber threats faced by Indian businesses?
Which government organizations in India handle cybersecurity threats?
What laws protect users from cyber attacks in India?
How do hackers steal personal data during cyber attacks?
What are the warning signs of a cyber attack?
How can businesses detect cyber attacks early?
What are the best practices for preventing cyber attacks?
Latest Updates & Articles
Stay Connected !! To check out what is happening at EIMT read our latest blogs and articles.







